Cyber Hygiene 101
Keeping your online presence secure and healthy is crucial, especially in the workplace. Neglecting proper cyber hygiene practices can lead to data breaches, malware infections, and other online security threats that can compromise confidential information. But don’t worry; here at Masser Technologies, we have compiled six must-have practices for maintaining an excellent cyber hygiene environment. So please sit back and relax (continue reading) as we dive in.
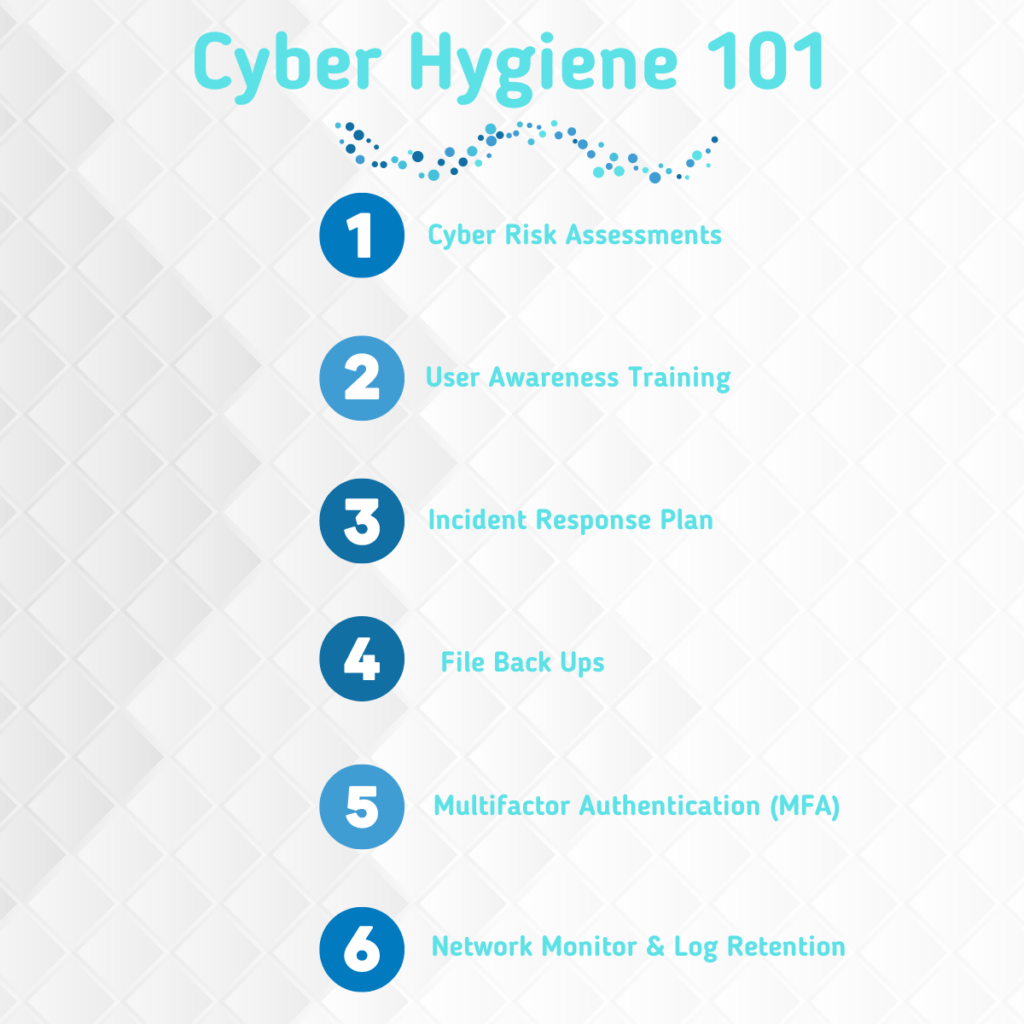
If you saw our graphic in this article, you probably figured out what those six practices are, so let’s expand. These practices are essential to maintain the health and security of users, devices, networks, and data. They also help comply with requirements such as PCI, HIPAA, and other regulatory compliance frameworks. Cybersecurity incidents can bypass weak defenses, infiltrate systems, and cause disruption to internal operations. While many companies invest in security measures to detect data breaches, fewer adopt a preventive approach. By assessing cybersecurity hygiene as part of an ongoing risk management strategy, companies can detect and prevent more significant problems. This is similar to an annual medical check-up. Detecting issues early can prevent them from becoming more significant. Masser Technologies provides all six practices to our clients to fortify defenses and detect problems early on before a serious incident occurs:
Keeping your online presence secure and healthy is crucial, especially in the workplace. Neglecting proper cyber hygiene practices can lead to data breaches, malware infections, and other online security threats that can compromise confidential information. But don’t worry; here at Masser Technologies, we have compiled six must-have practices for maintaining an excellent cyber hygiene environment. So please sit back and relax (continue reading) as we dive in.
If you saw our graphic in this article, you probably figured out what those six practices are, so let’s expand. These practices are essential to maintain the health and security of users, devices, networks, and data. They also help comply with requirements such as PCI, HIPAA, and other regulatory compliance frameworks. Cybersecurity incidents can bypass weak defenses, infiltrate systems, and cause disruption to internal operations. While many companies invest in security measures to detect data breaches, fewer adopt a preventive approach. By assessing cybersecurity hygiene as part of an ongoing risk management strategy, companies can detect and prevent more significant problems. This is similar to an annual medical check-up. Detecting issues early can prevent them from becoming more significant. Masser Technologies provides all six practices to our clients to fortify defenses and detect problems early on before a serious incident occurs:
1. Cyber Risk Assessments: Periodic assessments of your cybersecurity infrastructure, like an annual physical, can help inform your preventive core plan and pinpoint emerging sources of vulnerability.
2. User Awareness Training: Just like diet and exercise are essential to physical health, employees should be trained to follow your organization’s data breach prevention and response procedures for cybersecurity health.
3. Incident Response Plan: Having an incident response plan is like knowing the proper treatment when you get sick. It can improve recoverability and limit the severity and duration of the incident.
4. Back-Up Files: Managed and offline backups protect your data from cyber threats. This means that when your systems are infiltrated, you don’t have to stop operations while trying to recover your systems or data.
5. Multi-Factor Authentication (MFA): MFA makes accessing your systems and information harder for the average criminal. The less enticing you are as a target, the more likely thieves will choose another victim.
6. Network Monitor & Log Retention: 24×7 monitoring enhances protection against attacks by rapidly identifying data breaches, infections, or potential disruptions in real-time while retaining logs for analysis and compliance.
3. Incident Response Plan: Having an incident response plan is like knowing the proper treatment when you get sick. It can improve recoverability and limit the severity and duration of the incident.
4. Back-Up Files: Managed and offline backups protect your data from cyber threats. This means that when your systems are infiltrated, you don’t have to stop operations while trying to recover your systems or data.
5. Multi-Factor Authentication (MFA): MFA makes accessing your systems and information harder for the average criminal. The less enticing you are as a target, the more likely thieves will choose another victim.
6. Network Monitor & Log Retention: 24×7 monitoring enhances protection against attacks by rapidly identifying data breaches, infections, or potential disruptions in real-time while retaining logs for analysis and compliance.